We develope intelligent software solutions for your company

jazzyLanTalk
jazzyLanTalk is our new software for communication in the local network.
- jazzyLanTalk is secure thanks to end-to-end encryption.
- jazzyLanTalk is user-friendly thanks to the simple and intuitive user interface.
- jazzyLanTalk is flexible and allows you to send and receive messages and documents at any workstation.
- jazzyLanTalk is cost-effective and does not require the purchase of expensive hardware or software.
- jazzyLanTalk is scalable and can easily be expanded to include users and functions.

jazzyWeb
Internet presences and web applications based on the Python framework web.py.
Adapted to: Effective, fast hosting with your own IP if desired.
- jazzyWeb offers excellent design
- jazzyWeb Fast loading speeds thanks to lean code
- jazzyWeb Security through content security policy and design
- jazzyWeb 100% technical SEO
- jazzyWeb Mobile first
- jazzyWeb Editable pages and content
- jazzyWeb Contact forms, sliders, gallery and much more.

jazzyMaps
Map integration and routing with the open source project OpenStreetMap (OSM), the alternative to Google Maps:
- jazzyMaps without complicated key management.
- jazzyMaps at no additional cost.
- jazzyMaps supported and kept up to date by a large community.
Example:
We provide OSM geo information for websites, shops and web applications.

jazzyWeb Multilingual
Expand your customer base and make your web project international.
We offer multilingualism for our jazzyWeb sites with automatic translation of controls and content. The translations can be edited in the backend of the website, and we offer a wide range of languages.

jazzyBabelChat
Our "Babelfish" chat
The Babelfish comes from Douglas Adams' science fiction novel "The Hitchhiker's Guide to the Galaxy." It's a small, yellow fish that you stick in your ear and translates into all languages.
With jazzyBabelChat we have developed a simple written chat system that automatically translates into the user's language in real time. This allows users to communicate with foreign-language users in their own language.
We provide individual services for your company

Web design and e-commerce
We create high-performance, representative, responsive websites and web shops. Search engine optimization (SEO) is a given.
We develop shop interfaces, implement drop shipping, write plugins and themes for Wordpress, JTL Shop, Prestashop, Shopware. We integrate payment service providers and other services.
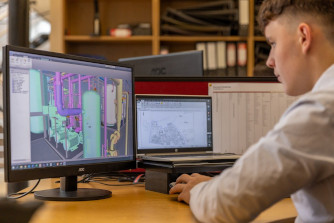
Software development
We develop software for workstations, networks and the Internet: Tailor-made business software from container management to order and customer management to small tools that make your life easier.
We are specialists in data management, conversion and migration. Data visualization and interface development. We connect worlds.

IT - Security and data protection
We support you with prevention and emergency assistance. A content security policy and SSL encryption are the basic requirements for securing your websites against attacks.
We harden and monitor your Linux server and prevent form spam. We support you with email and data encryption.
Data protection is important to us. We ensure GDPR compliance.
Linux servers and web hosting
We set up dedicated and virtual Debian Linux servers with database, mail and web server. We take care of maintenance, install and configure software packages and help with problems.
We also offer hosting for servers, websites or web shops. With us you will find personal support.
Talk to us and let us create an individual offer tailored to your needs.

Advice and support
Jazzy-Software offers individual, state-of-the-art consulting and services. You benefit from more than 25 years of experience in the IT sector. We work remotely and protect the environment and your wallet.
We support you with our know-how, from solving small everyday problems such as software installation and configuration to providing professional support for your planning and decision-making processes.

Chat for business partners and interested parties
We have also set up a jazzyBabelChat for our customers.
You will be activated immediately and can then chat with us in your language. Please feel free to suggest a date for an initial consultation. We take our time. Free of charge and without obligation for you.
We look forward to seeing you.